 Source: https://en.yeeply.com/blog/internet-of-things-26-billion-devices/
Source: https://en.yeeply.com/blog/internet-of-things-26-billion-devices/
1. What is IoT?
The Internet of Things (IoT) is an emerging concept, especially in the last decade, which refers to the technology of connecting objects and devices over the Internet, autonomously gathering information, performing analysis, and providing services to the users. About 26 billion IoT devices are installed by the year 2020.
However, IoT is actually not a novel concept as the original idea dated back to the 1960s when it was called pervasive computing or embedded Internet. In 1999, Kevin Ashton was the first person to introduce the term “IoT” while promoting Radio Frequency Identification (RFID), a technology that involves automatic identification and data capture.
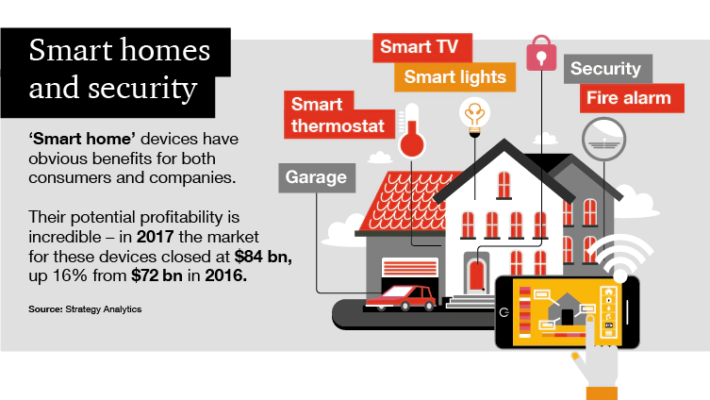
The existence and development of IoT were made possible thanks to the evolution of other technologies such as low-cost sensors, cloud computing platforms, machine learning, artificial intelligence, and even 5G in recent years. IoT witnessed a popularity explosion since 2010 when innovative technologies like smart wearables, smart agriculture, smart home, and security were introduced. The biggest advantage of IoT is its diverse functionalities since it can be applied in both industry and household appliances with various sizes and costs.
 Source: https://www.pwc.co.uk/services/risk/technology-data-analytics/data-protection/insights/the-internet-of-things-is-it-just-about-gdpr.html
Source: https://www.pwc.co.uk/services/risk/technology-data-analytics/data-protection/insights/the-internet-of-things-is-it-just-about-gdpr.html
2. How is IoT implemented in our life?
There are two main components in every IoT system, one of them is the Sensor Networks which consist of low-power, reliable sensors that monitor the environment and record the specified data. Then there is Smart Control which is capable of managing the data and providing useful services to the users.
One of the most notable applications of IoT is Smart home and security. With sensors like thermostats, motion sensors, or brightness and humidity detectors embedded in household appliances and connected to a Smart Control hub, you can monitor and control miscellaneous devices simultaneously.
Source: https://www.pwc.co.uk/services/risk/technology-data-analytics/data-protection/insights/the-internet-of-things-is-it-just-about-gdpr.html
But as the IoT business grows in size and value, concerns about security and personal data protection are raised among users and specialists.
3. What are the biggest IoT security concerns?
Even though it is the fundamental principle and what made this technology successful, the data-driven characteristic of IoT poses a serious threat to the system and its users. By connecting your devices to the Internet, you are opening them up to potential privacy risks.
Unlike traditional devices, smart objects can collect and store information on your usage, habits, and preferences on local devices or on the network, sometimes without your concern. These data along with other valuable information like your bank accounts, social media accounts, and data on your smartphone or personal computer could be accessible to a criminal.
Even when the devices are thought to be safe from cybersecurity threats, the fact that they can gather sensitive information without human supervision makes people think twice before installing them.
 Source: https://www.kaspersky.com/resource-center/threats/how-safe-is-your-smart-home
Source: https://www.kaspersky.com/resource-center/threats/how-safe-is-your-smart-home
4. How to protect personal data while implementing IoT?
From the perspective of the manufacturers, it is advisable to follow official requirements and standards relating to security and personal data protection such as the General Data Protection Regulation (GDPR) and the ePrivacy Regulation. These legislations obligate IoT manufacturers to provide users with detailed and comprehensive information about their collected and processed data.
 Source: https://www.i-scoop.eu/gdpr/eu-eprivacy-regulation/
Source: https://www.i-scoop.eu/gdpr/eu-eprivacy-regulation/
Furthermore, it is important to address machine-to-machine communication (excluding the application layer), which has been categorized as an electronic communications service by the ePrivacy Regulation. As a result, users’ consent would be required when transmitting data from one IoT device to another.
Besides the legislative issues, upgrading the system continually is also needed as criminals may attempt to interfere with the system with more and more advanced techniques.
Authentication mechanisms such as two-factor authentication, digital certificates, and biometrics should be implemented for multiple-user devices. The use of data encryption and API security methods should become standard to protect the privacy of users and prevent interference.
 Source: https://www.kaspersky.com/resource-center/threats/how-safe-is-your-smart-home
Source: https://www.kaspersky.com/resource-center/threats/how-safe-is-your-smart-home
For the customers, ensure that your devices are password protected when available.
Protect your smartphone and personal computer which you use to control the IoT system from cybersecurity threats as they can be utilized to gain access to IoT devices and manipulate them.
Keep your devices up to date, update your firmware and software regularly and use strong security software.
Purchase your devices from prestigious manufacturers and read the manual carefully to understand how safe they are, what security threats could emerge, and what kind of information is being collected from you.
5. Conclusion
IoT and personal data protection improve the living conditions of individuals and benefits enterprises in many ways. Security and personal data protection however remain issues as they are not yet adequately addressed. Nevertheless, solutions and improvements are being proposed and implemented, so we can believe in a bright future for this technology.
- References
https://www.kaspersky.com/resource-center/threats/how-safe-is-your-smart-home
https://www.pwc.co.uk/services/risk/technology-data-analytics/data-protection/insights/the-internet-of-things-is-it-just-about-gdpr.html
https://www.mdpi.com/2076-3417/10/12/4102
Internet of Things: soon connecting the world by 26+ billion devices
Top 10 IoT Security Solutions for the Most Common IoT Security Issues
IoT Update: The E-Privacy Regulation – Impact on the IoT market
